ARCHIVE
betakit

Navigating Privacy Concerns in the Age of IoT: Striking a Balance Between Innovation and Data Protection
In an increasingly interconnected world, the Internet of Things (IoT) promises unparalleled convenience, efficiency, and innovation. From smart homes and wearable devices to industrial sensors and connected vehicles, IoT technologies have permeated nearly every aspect of our lives, revolutionizing how…

Harnessing the Potential of Edge Computing: Exploring Application and Advantages
In today's fast-paced technological landscape, data is the driving force behind innovation and progress. Every sector, from manufacturing to healthcare, transportation, and retail, heavily relies on vast amounts of data to streamline operations and achieve growth. However, traditional centralized computing…

Global Secure Solutions Partners with Cloud Range to Revolutionize Cybersecurity Training
Published on MyJoyOnline.com 22 January 2020 Global Secure Solutions (GSS) has made a groundbreaking move by announcing its partnership with Cloud Range, ushering in a new era in cybersecurity training. Cloud Range, a simulation-based cyber defense training platform, is now offering…

Global Secure Solutions Unveils Prometheus Shield: A Game-Changing Cybersecurity Platform
Published on MyJoyOnline.com 4 October 2021 In a major development, Global Secure Solutions (GSS) has introduced Prometheus Shield, a state-of-the-art security management platform designed to revolutionize cybersecurity. The platform offers unparalleled visibility into critical areas within an organization's IT infrastructure, providing…

Global Secure Solutions Recognized as a Leading Cybersecurity Provider in 2023 by Enterprise Viewpoint
Published on Enterprise Viewpoint - 2023 We are excited to spotlight Global Secure Solutions, acknowledged by Enterprise Viewpoint as a standout cybersecurity provider for 2023. In a world where cyber threats continue to evolve, Global Secure Solutions takes center stage…

Safeguarding the Digital Frontier: Global Secure Solutions Leads the Charge in Cybersecurity
Published on Enterprise Viewpoint-July 11, 2023 Enterprise Viewpoint presents a comprehensive overview of the evolving cybersecurity landscape and the critical role played by Global Secure Solutions. In an era defined by advancing threats and technological complexities, Global Secure Solutions stands…
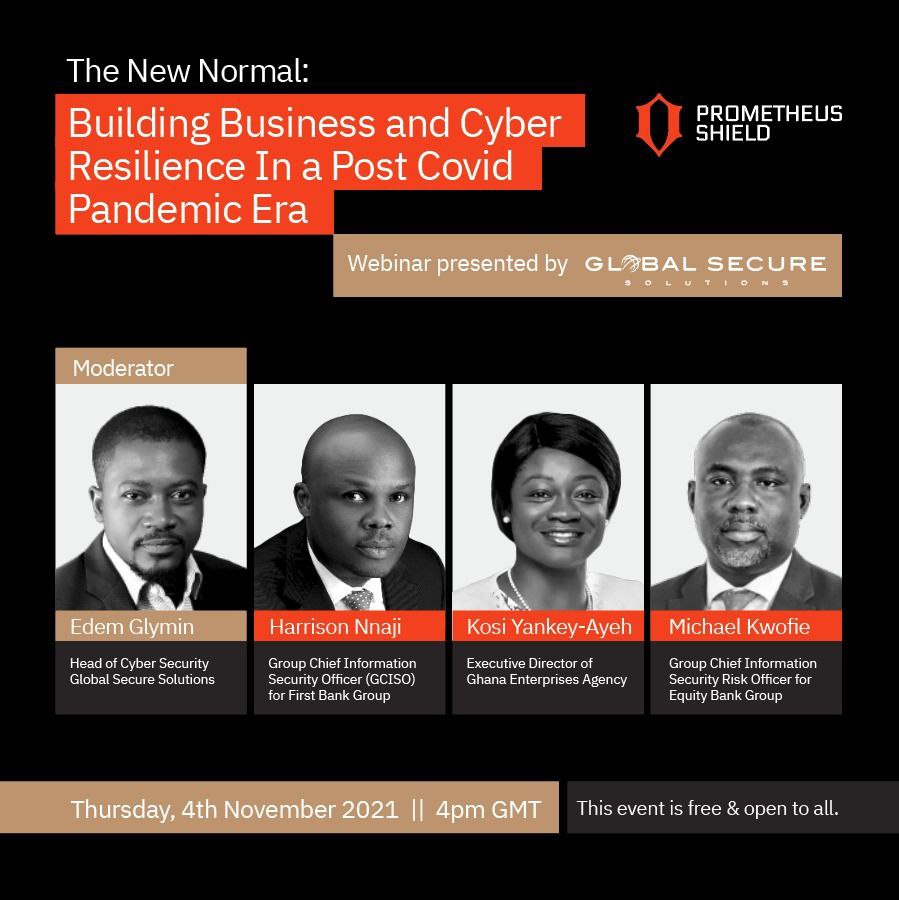
THE NEW NORMAL: BUILDING BUSINESS AND CYBER RESILIENCE IN A POST COVID PANDEMIC ERA (Recorded Webinar)
The aim of this webinar is to create awareness for stakeholders in the business community on the need to be more proactive and identify different solutions to maintaining continuity of business operations in the face of increasing cybersecurity challenges.
Global Secure Solutions Ghana Limited launches managed cybersecurity services for SMEs
Work From Home Environments Create New Opportunities for Cybercriminals Accra, Labone: October 26, 2021 – Businesses entered 2020 with plans for continued growth and innovation, with a global market economy poised for growth. COVID-19 and the related economic downturn disrupted…
6 Common Phishing Attacks and How to Protect Against Them
By: David Bisson Source: Tripwire.com Phishing attacks continue to play a dominant role in the digital threat landscape. In its 2020 Data Breach Investigations Report (DBIR), for instance, Verizon Enterprise found that phishing was the second topmost threat action variety in security…