Qualys Multi-Vector EDR
Bringing the scale, accuracy and unifying power of the Qualys Cloud Platform to EDR.
E-mail our sales team
or call us at +233 (0) 243 335 025
A new multi-vector approach to Endpoint Detection and Response
Traditional endpoint detection and response (EDR) solutions focus only on endpoint activity to detect attacks. As a result, they lack the full context to analyze attacks accurately. This leads to an incomplete picture and a high rate of false positives and negatives, requiring organizations to use multiple point solutions and large incident response teams.
Qualys fills the gaps by bringing a new multi-vector approach and the unifying power of its highly scalable Cloud Platform to EDR, providing vital context and comprehensive visibility to the entire attack chain, from prevention to detection to response.
Qualys Multi-Vector EDR unifies different context vectors like asset discovery, rich normalized software inventory, end-of-life visibility, vulnerabilities and exploits, misconfigurations, in-depth endpoint telemetry, and network reachability with a powerful backend to correlate it all for accurate assessment, detection and response – all in a single, cloud-based app.
Lightweight Qualys Cloud Agents (<3MB) power the app and continuously collect and stream data to the Qualys Cloud Platform, where the information is correlated, enriched and prioritized for real-time visibility into everything that’s happening on the endpoint and the surrounding network. Whether it is killing processes, quarantining files or endpoints, patching vulnerabilities, removing exploits, fixing misconfigurations or uninstalling software, our singular agent can do it all.
Why Choose Qualys EDR?
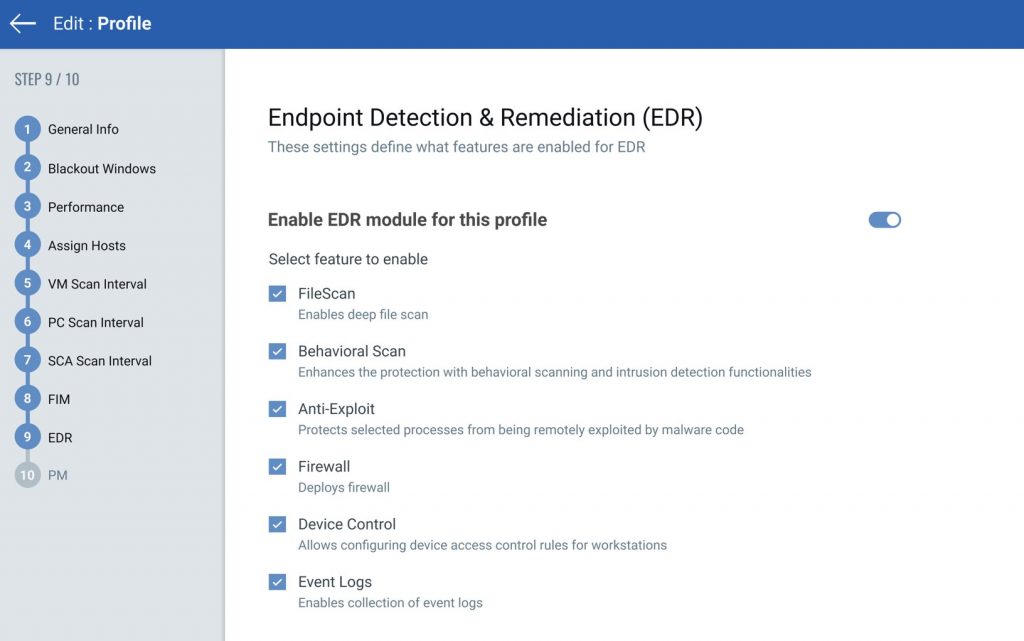
Consolidate your stack
Qualys Multi-Vector EDR leverages the Qualys Cloud Platform to collect and correlate vast amounts of IT, security and compliance data. By using Qualys, adding more functionality and more coverage is as easy as checking a box. Configure and administer all your tools in one place without adding complexity.
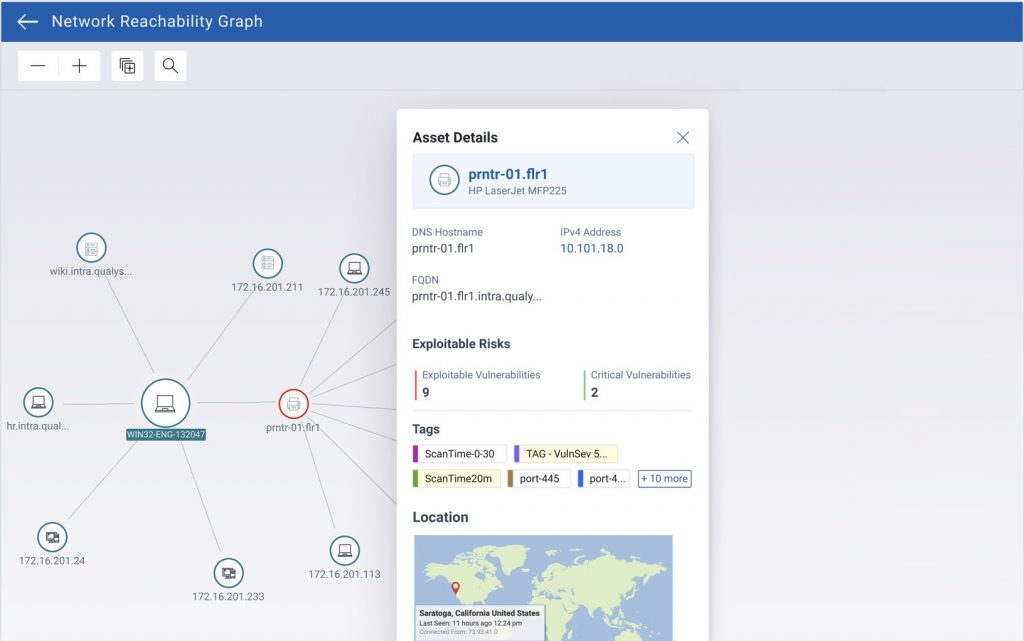
Real-time visibility into asset inventory and telemetry
You can’t secure what you cannot see or don’t know! With Global IT Asset Inventory integrated into Qualys Multi-Vector EDR, it automatically discovers and classifies all IT assets including endpoints using multiple Qualys sensors such as cloud agents, network scanners and passive sensors, providing deep visibility into asset telemetry. Additionally, it automatically organizes assets with dynamic asset tagging, enabling organizations to quickly rollout EDR across their entire global hybrid environment – eliminating endpoint blind spots.
Continuous detection of exploitable vulnerabilities and misconfigurations
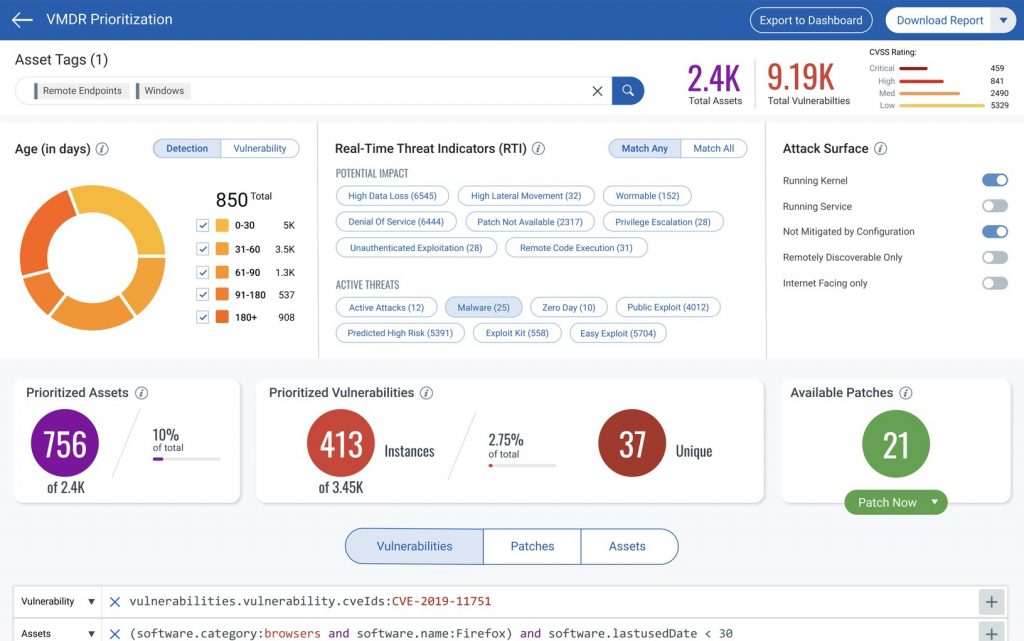
Traditional EDR tools operate without the context of open vulnerabilities, misconfigurations and missing patches, which is often why malicious activities succeed on endpoints. By enabling Qualys VMDR (Vulnerability Management, Detection and Response) with policy compliance add-ons, Qualys Multi-Vector EDR continuously detects CVEs with exploits available in the wild, as well as exploitable security misconfigurations, and automatically prioritizes them for one-click patching or remediation – all in a single workflow!
Built-in anti-malware technology
With native integration of industry-leading anti-malware protection technology, Qualys Multi-Vector EDR eliminates the overhead of managing traditional anti-virus solutions. Qualys Multi-Vector EDR provides multi-layered anti-malware, anti-phishing and anti-exploit protection with application behavior scanning so that all malicious attacks are accurately detected and automatically blocked on the endpoint within seconds.
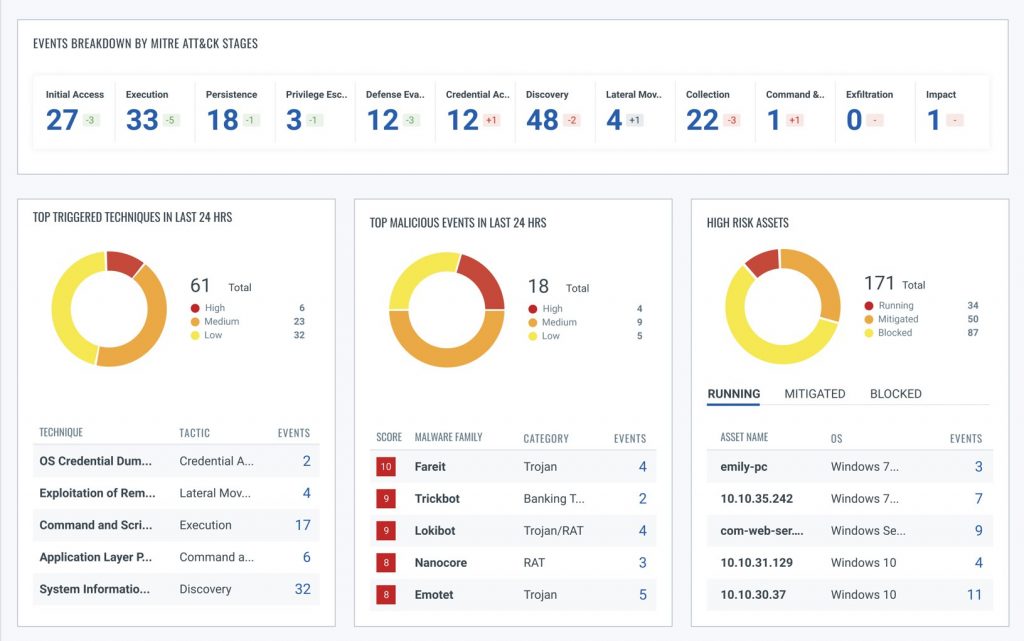
MITRE ATT&CK™ driven threat detection, analytics and threat intelligence
The MITRE Enterprise Adversarial Tactics, Techniques and Common Knowledge (ATT&CK) framework is a curated knowledge base and a model for cyber-adversary behavior that reflects the various phases of the attack lifecycle and the platforms attackers are known to target. Threat hunters, red teamers, and defenders use this behavior model to detect and classify attacks and assess an organization’s risk. Qualys Multi-Vector EDR provides in-house researched detections and enrichments from other Qualys apps as well as native integration of threat intelligence feeds from leading third-party sources.
Unified security incident investigation and alerting
Qualys Multi-Vector EDR collates vast amounts of IT, security and compliance data collected from its hybrid sensors and augments it with threat intelligence from multiple external sources. It also enriches the data with process graphs to visualize attack paths, thus enabling security teams to unify their incident investigation, reduce false positive and negatives, and prioritize incidents for the appropriate response. Security teams can also monitor and investigate threats through simple, intuitive workflows via the native UI or APIs.
Real-time, multi-layered mitigation and response
Qualys Multi-Vector EDR’s multi-layered response strategies enable security teams to remediate threats in real-time while maintaining the business continuity of the endpoints. With zero-day exploits and ransomware attacks, it is vital to track advisories through dynamic dashboards, set email alert rules, investigate security incidents for details, and contain attacks through speedy response actions. Unlike other cloud-based EDR solutions, Qualys Multi-Vector EDR not only supports appropriate response capabilities on the endpoints, but also blocks exploits, known malware and malicious processes in real time.
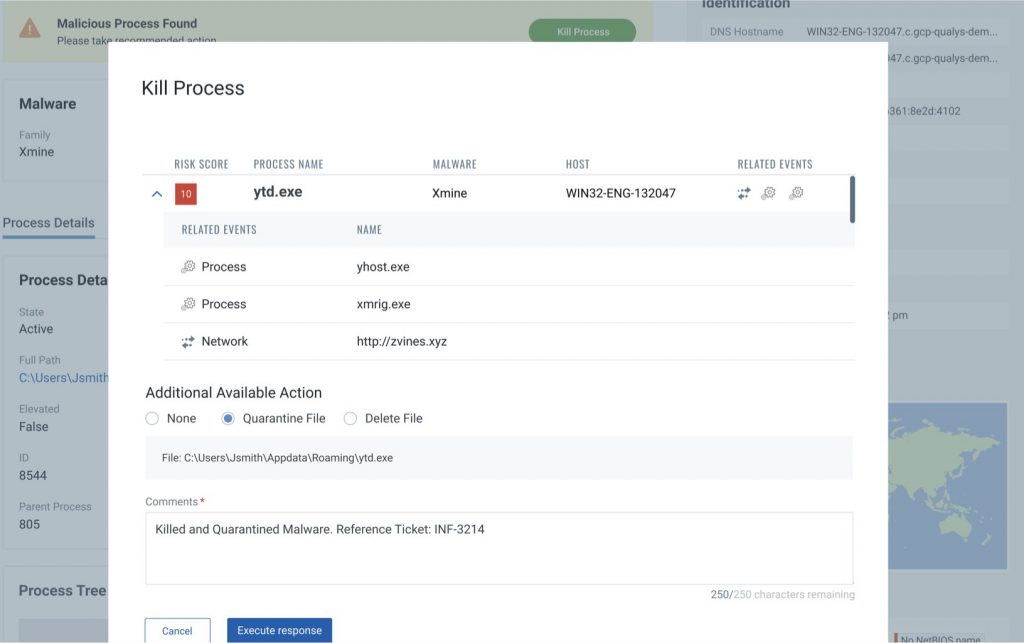
Orchestration of prevention such as patching, remediation and more!
Qualys Multi-Vector EDR is the only platform that provides a host of prevention strategies such as automated patching, misconfiguration remediation, and removal of software to ensure endpoints cannot be victimized again. Qualys Multi-Vector EDR also provides a comprehensive list of all hosts with exploitable vulnerabilities and misconfigurations, and end-of-life and blacklisted software. Additionally, it provides the ability to orchestrate patching and remediation jobs to secure the entire environment. That way your security teams can concentrate on the advanced threats rather than the attacks happening via exploitable vulnerabilities and misconfigurations.
The security of your organization is our business
Phone Number(s)
🇬🇭 +233 (0) 243 335 025
🇬🇭 +233 (0) 55 652 6210
🇬🇭 +233 (0) 243 335 025 ( )
)
Email Address
info@globalsecuresolutions.com
Local Address
H/No. 17 Peter Ala Adjetey Avenue, North Labone, Accra – Ghana.




