Latest news & articles
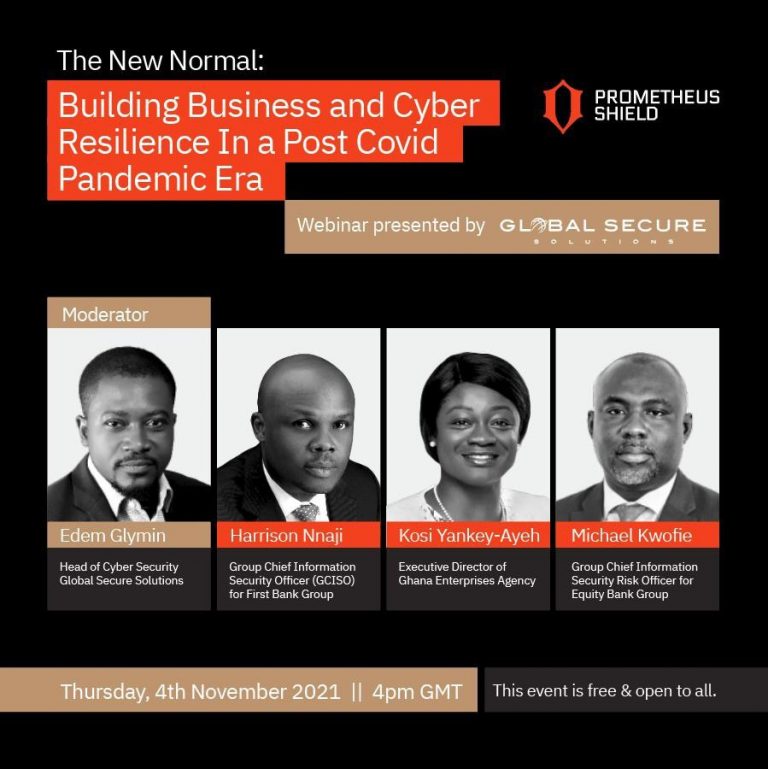
THE NEW NORMAL: BUILDING BUSINESS AND CYBER RESILIENCE IN A POST COVID PANDEMIC ERA (Recorded Webinar)
The aim of this webinar is to create awareness for stakeholders in the business community on the need to be…
Global Secure Solutions Ghana Limited launches managed cybersecurity services for SMEs
Work From Home Environments Create New Opportunities for Cybercriminals Accra, Labone: October 26, 2021 – Businesses entered 2020 with plans…
6 Common Phishing Attacks and How to Protect Against Them
By: David Bisson Source: Tripwire.com Phishing attacks continue to play a dominant role in the digital threat landscape. In its 2020…
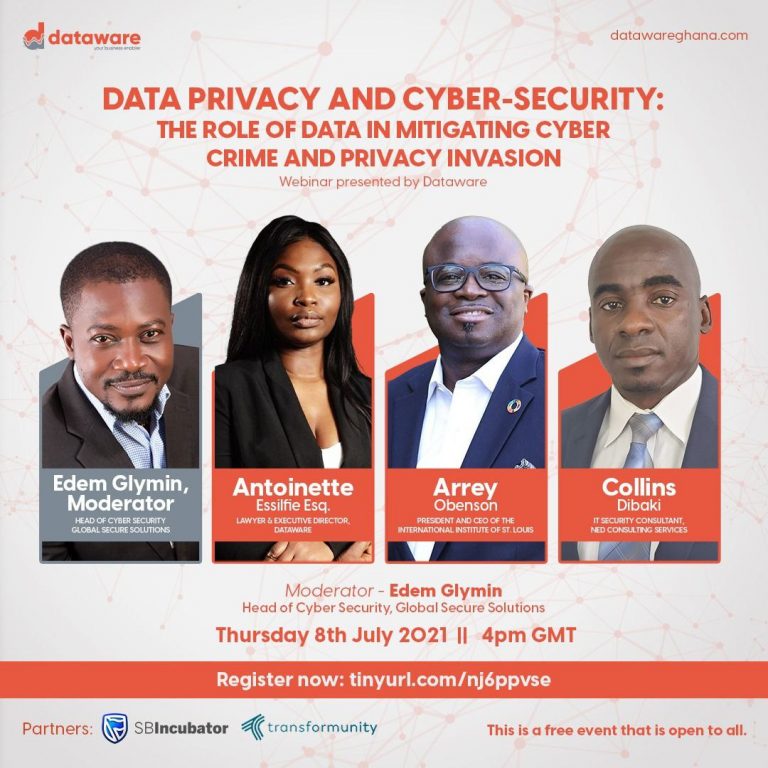
DATA PRIVACY AND CYBER-SECURITY: THE ROLE OF DATA IN MITIGATING CYBER CRIME AND PRIVACY INVASION (Recorded Webinar)
Watch Webinar here
Detailed Threat Analysis of Shamoon 2.0 Malware
DevOps. Machine learning. Faster decision making. The biggest trends in IT are helping us speed release cycles, get more insights,…
How Simulation Training is becoming an Integral part of Cyber Preparedness. (Recorded Webinar)
https://player.vimeo.com/video/428224232 Defining and testing a cyber incident response plan is a highly effective way of reducing the impact and duration…
COVID-19 | The Cybersecurity Effect of the Pandemic
By: Edem Glymin, Lead security and risk consultant for Global Secure Solutions Ghana Limited. How did we get here? Suddenly…
Hackers Are Selling a Critical Zoom Zero-Day Exploit for $500,000
By Lorenzo Franceschi-Bicchierai , Source: Motherboad, Tech by VICE Hackers are selling two critical vulnerabilities for the video conferencing software…
Vietnam-linked hackers targeted Chinese government over coronavirus response: researchers
By: Jack Stubbs, Raphael Satter Additional reporting by Muyu Xu in Beijing and James Pearson in Hanoi; Editing by Richard…




